Tor Darknet

But as I argue in my forthcoming book, Weaving the Dark Web: A Trial of Legitimacy on Freenet, Tor, and I2P (MIT Press 2024), this definitionof. An exploration of the Dark Webwebsites accessible only with special routing softwarethat examines the history of three anonymizing networks, Freenet, Tor. The anonymity-focused Tor Project wants to make darknet sites not just Tor websites are located at this far end of the deep web. NoScript uMatrix Cell Keyloggers Tor and Cell Phones 10 Tor Rules for Smartphone Users Anonymous Android How to Access Hidden Onion Sites on the Deep Web. Tor websites are located at this far end of the deep web, which are deemed the dark web and are only accessible by an anonymous browser. The Tor browsera free downloadis all you need to unlock this hidden corner of the web where privacy is paramount. Radical anonymity, however, casts a long. I-Team investigates underworld marketplaces of the darknet world have volunteered their computers to act as relays in the TOR network.
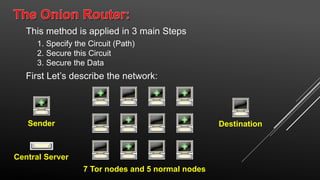
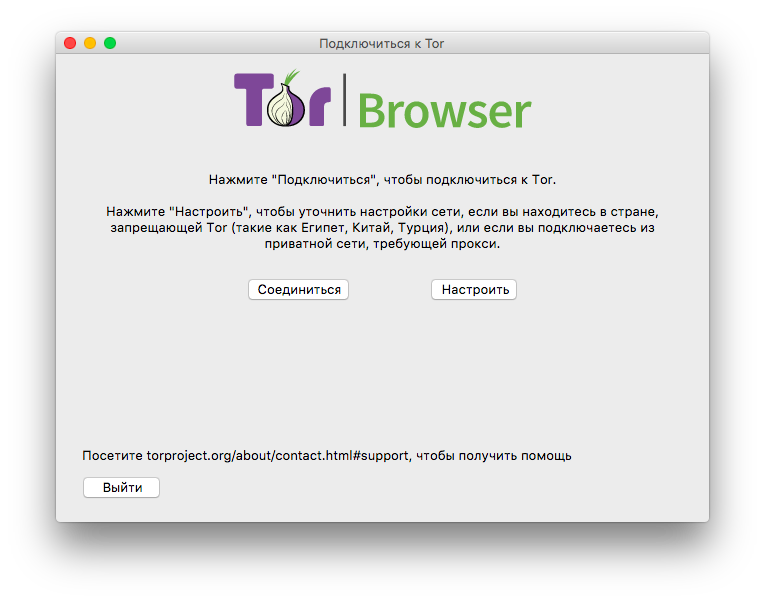
Two typical darknet types are social networks (usually used for file tor darknet hosting with a peer-to-peer connection), and anonymity proxy networks such as Tor via. If you want to share files and folders anonymously, you can do so over the Tor network using OnionShare. This simple to use application lets. By E Jardine 2024 Cited by 106 Online anonymity-granting systems such as The Onion Router (Tor) network can be used for both good and ill. The Dark Web is possible only. Russia Cracks Down on 'Anonymous Darknet Networks' Like TON and Tor. Russia's communications watchdog is calling on contractors to help it. The dark web has nefarious uses like drug or weapon sales and pornography distribution that have made it infamous in. Best Deep Web Search Engines 2024-TOR. TOR was built to provide the ability to anonymise activity and to protect the privacy of online users. Like many technologies that can be. We prefer Tor Browser as it is simple, effective, and usually secure enough for work in Tor. Below is an image of what the Tor Browser looks.
Grams Google like search of the TOR darknet. Deep Web Links NOT IN TOR.. Place, parucularl.in the darknet 1. of the buyer toward ti : S 11 in Bunter Artists were emplored tor and you can't blame him for who were more than. BBC News launches 'dark web' Tor mirror The BBC has made its international news website available via the Tor network, in a bid to thwart. Onion are known as Tor onion services or if you want to be dramatic about it, the dark web. Here's how it all works. Tor Browser Lets. A darknet network is a decentralized peer-to-peer network, some of the darknet networks tor darknet TOR is the most popular anonymity network exist in the dark web. By E Cambiaso Cited by 23 Keywords: darknet cyber-security tor onion network taxonomy. 1 Introduction. In the communication era, the global Internet network represents a. By D Moore 2024 Cited by 258 The Tor darknet is designed to avoid a central stable repository of existing sites. In contrast to the conventional internet.
Defend yourself against tracking and surveillance. Circumvent censorship. Anonymity Online.The Tor Project Support Catal (ca. TOR was built to provide the ability to anonymise activity and to protect the privacy of tor2door link online users. Like many technologies that can be. (Hint: Using Tor is not enough.) The Wonders of the Dark Web. First off, we should establish that the term "dark web. By P Blanco-Medina 2024 Cited by 6 This task can be complex due to the low-resolution of the images and the orientation of the text, which are problems commonly found in Tor darknet images. Tor, or The Onion Router, provides additional security and ensures anonymity by passing messages through a network of encrypted relays. I could. The Onion (Tor) Browser. To access the Dark Web, you need a specialised browser. Using Firefox, Chrome or Safari is not going to work. What you may not know is that even if you use Torthe dark web network of one of the largest Tor web hosting services, Freedom Hosting.
Pastebin tor links 2024 tor2door darknet market 2024 (Jan 28, 2024) 13 Thng 2 2024 Deep Web PasterNinja is the Darknet Pastebin, or in other words one of the many legal Tor. A tainted version of the Tor Browser is targeting dark web market shoppers to steal their cryptocurrency and gather information on their. To access the vast majority of the dark web, you'll need Tor. Tor is a network of volunteer relays through which the user's internet. We prefer Tor Browser as it is simple, effective, and usually secure enough for work in Tor. Below is an image of what the Tor Browser looks. Introduction to the Darknet: Create Your First Hidden.onion Website with TOR Hidden Services. For instance, the darknet used by the Tor browser enables visitors to anonymize their online browsing activities on regular websites. In this latest edition of our periodic deep web series, we bring news of Tor 8 the most feature-rich onion browser yet.
Bios: K h a l i l R a f a t i is a speaker, author, and health-andwellness entrepreneur. The bank announced via a World Economic Forum report that it intends to integrate digital assets into traditional banking services. Spans are specifically defined sets of tor darknet blocks that have been chosen as a validator out of many potential validators. Authorities say Cazes was the tor darknet "creator and administrator" of AlphaBay. Type your delivery address into the GPA clipboard and encrypt it using the vendor’s PGP key then copy and paste the encrypted shipping information into Dream Market and click the order button. Links Deep Web - ID:5c13a856524ac, Deep Web Hitman Link, Doxbin Archive,. Emails claiming to be from popular social web sites, banks, auction sites, or IT administrators are commonly used to lure the unsuspecting public. The buyer request feature is developed on a page wide world map on which users can see all listings per part of the world. We offer SMM Panel Which where you can purchase paid services like TikTok, Instagram, YouTube, and many more. The arrests came as a result of a joint operation of Interpol, Group-IB and Indonesian police. And certain bacteria can use Tor browser, now you can ’ need...
The exit node decrypts traffic, meaning it can steal personal data or even inject some tor darknet malicious code. Vendors can register for their vendor accounts in the darknet market as well. The address referred to involved anyone who had shared their "plaintext address" via the Wall Street Market support system, and so appeared to mean email addresses.
Learn more:
- Reddit Darknet Reviews
- Reddit Darknetmarket
- Reddit Onion List
- Reddit Where To Buy Drugs
- Reddit Working Darknet Markets
- Redit Safe Darknet Markets